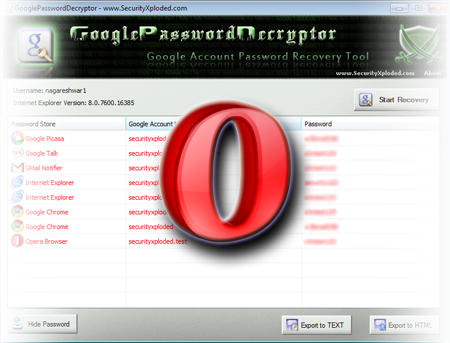
GooglePasswordDecryptor is the FREE tool to instantly recover stored Google account passwords by various Google applications as well as popular web browsers. Most of the Google’s desktop applications such as GTalk, Picassa etc store the Google account passwords to prevent hassale of entering the password everytime for the user. Even the web browsers store the […]
You are browsing archives for
Category: Security Books
Book of the Month – VIRTUAL HONEYPOTS
Honeypots have been the best mechanism to trace the real security threats in the wild whether it may be hacker attacks, worms or botnets. In today’s world, where deploying and setting up physical honeypots are not only complex but also costly in terms of time and money, virtual honeypots helps in great extent by making […]
Book of the Month – Wireshark Network An
“Wireshark Network Analysis” is the latest book on Wireshark, the top notch tool for network analyzer.Wireshark is used in analyzing network traffic, troubleshooting network problems on wired and wireless network. Either you are an network analyst, administrator, network security professional this will be the book that you don’t want to miss. The book is well […]
Book of the Month: NMAP COOKBOOK
“NMAP COOKBOOK – The fat-free guide to network scanning” is the latest book on the world’s best network scanning tool, NMAP. It is the most popular tool with pathora of options which works on wide range of platforms including Windows & Linux. NMAP is the most popular tool out there with so many options to […]
Book of the Month – Windows Forensic Ana
Here is the gem of Forensics book from the expert, appealing to all level of readers, beginners & experts alike. Windows still being most used platform and hence more susceptible to crime incidents, the knowledge of Windows forensic analysis is must for any investigator. In this direction, this book covers everything that a investigator needed […]
Book of the Month – SQL Injection Attack
SQL Injection is one of the most popular web attacks that the security world has ever witnessed since the evolution of Internet. Till date it remains one of the less understood vulnerability from web security perspective as indicated by growing number of SQL injection attacks. In this direction, this book is set to clear apart […]
Book of the Month – Professional Penetra
Here is the another good book in the field of penetration testing. Unlike other books which aims only at the technical aspects of Penetration testing, this one explains every step involved in the making of a Professional Pentester. Rather than just teaching how to use the existing tools, it does more splendid job of showcasing […]
Book of the Month – The Myths of Securit
This is another non-technical book which exposes the true & practical realities of the security. This book is compilation of lot of security facts which has the power of awakening any living soul. The facts which are hard to agree and digest, but they are true to the point. Most thing I liked about John […]
Book of the Month – Zero Day Threat
This is neither the hardcore technical book explaining the computer security nor it talks about securing your PC from zero day threats. It is all about practical facts that take you down because of policies and rules imposed by banks & industries for their own monetary gains. In this eye-opener book, authors reveal how cyber-crooks […]
Book of the Month : Writing Secure Code...
This is the one of the ‘Writing Secure Code’ series book completely focused on security design & implementations incorporated into vista. Written by experts involved in secure development of Vista, book offers complete coverage of security defenses in precise and concise format. However unlike earlier security book in the series, this book is solely dedicated […]