Structured Exception Handling is a mechanism for handling both hardware and software exceptions in Windows OS. Structured exception handling enables us to have complete control over the handling of exceptions and it also provides support for debuggers as well. SEH exploitation is based on stack buffer overflow technique. It becomes easy to exploit a […]
You are browsing archives for
Category: Vulnerability Research
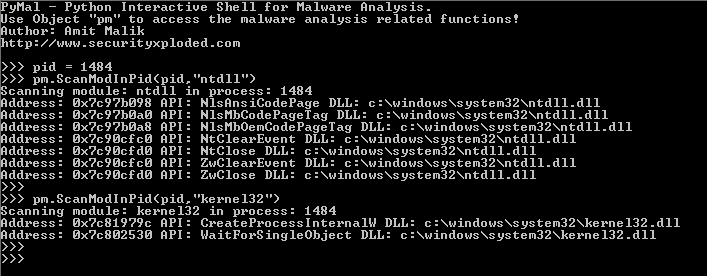
Bamital Analysis using Malpimp and Pymal
A couple of months ago, I released my two new tools Malpimp and PyMal for malware analysis. Malpimp aims at API tracing and PyMal is a general purpose malware analysis tool. In this blog I will discuss how to use both of them in malware analysis. As a case study I am using Bamital botnet […]
Reversing Training Session Part 11 – Exp
Here is the quick update on this month’s Local Security meet (SX/Null/G4H/owasp) where Amit has delivered one of his best session on ‘Practical Reversing VI – Exploit Development Advanced’. This is part of our ongoing FREE ‘Reversing & Malware Analysis Training’ started since our Jan 2012 meet. Today we had solid response from the crowd […]
Book of the Month – Metasploit: The Pene
It gives me great pleasure to review this book ‘Metasploit – The Penetration Tester’s Guide’, not only because it is written on most popular penetration testing framework but the way it is written doing complete justice to the title! . . Here is the core information about the book, Title: Metasploit: The Penetration Tester’s Guide […]
SX Impact – Developer Fixes Vulnerabilit
Few days back, we have published research article on “Vulnerable Facebook Applications” by Abhinav Singh, one of our active contributor. In this article, he has exposed how vulnerable Facebook Applications are and how they can breach the user’s credentials by citing the example of XSS vulnerability in “Name Meaning” Application. . . Today to our […]
Book of the Month – IDA PRO 2nd Edition
The best book on IDA PRO gets even better with second edition. This is one of those special books which does not need any review at all. The book stands on its own. . Since I have received the request from No Starch Press for special review of this book, here I will make an […]
‘Password Security’ Presentation at IIT
Here is brief capture of the security conference “Information Security Education & Awareness 2011” (ISEA) held at IIT Guwahati where I presented ‘Primer on Password Security’. This event was held as part of initiative to educate masses on growing trends and latest topics of information security. . On the first 2 days of the event, […]
Facebook Chief Security Officer to Keyno...
After the success of last year’s inaugural event, Hack In The Box Security Conference is taking over the Krasnapolsky once again from the 17th till the 20th of May. This deep knowledge security conference brings a unique mix of security professionals, researchers, law enforcement and members of the hacker underground under one roof, with the […]
Book of the Month – A Guide to Kernel Ex
Anyone into Vulnerability Research and Exploitation knows how hard it is to discover a Security Vulnerability and then develop a reliable exploit for it. Now consider taking it from user land to kernel, the near impossible thing to get your shoes in for the show. . In that context, ‘A Guide to Kernel Exploitation’ new […]
Book of the Month – Mobile Malware Attac
As mobile devices becoming more and more sophisticated with their computing power and memory, the attackers are slowing shifting their focus from PC to these Mobile devices. Unlike earlier generation of mobile devices, current mobile devices are as powerful as our computer systems with increased memory and performance along with built-in internet connectivity. All of […]

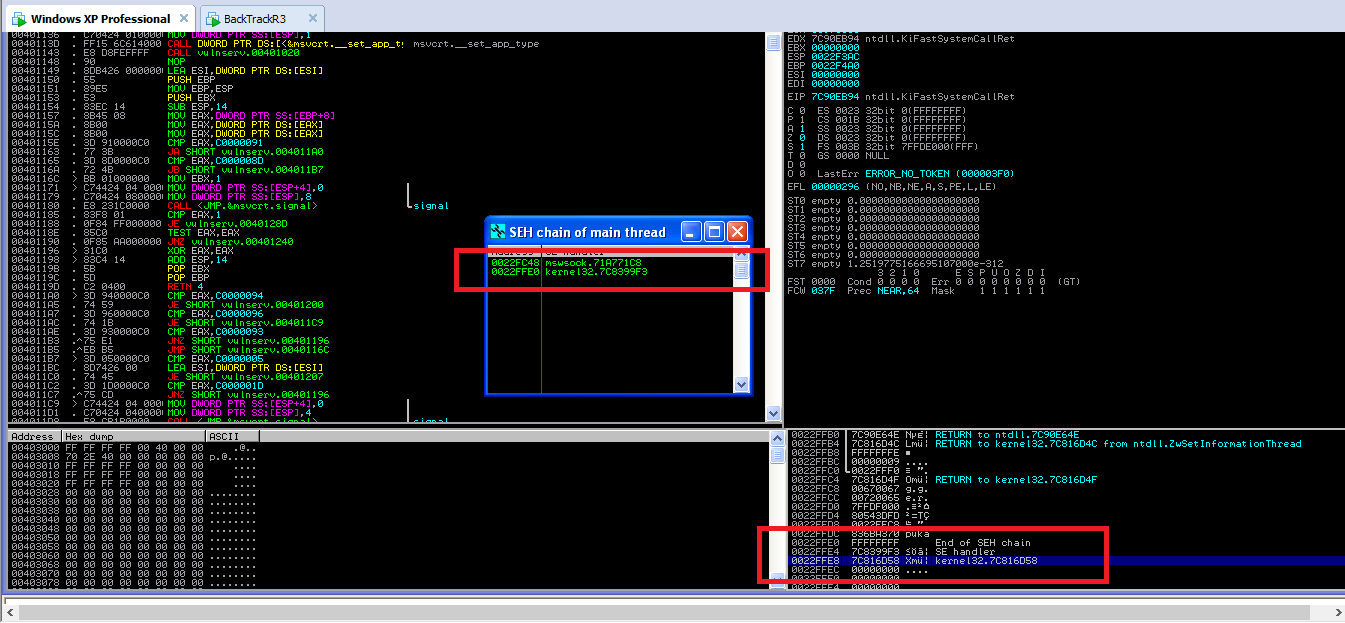
![Reversing Training Session Part 11 – Exploit Development [Advanced]](https://securityxploded.com/images/training-reversing-session9_main.jpg)