My new tool, SpyDLLRemover is released on the RootkitAnalytics website. This tool helps in detecting and deleting userland based rootkits which hide the processes and injected modules to prevent their detection from antirootkit softwares. Here is the snapshot of SpyDLLRemover detecting the hidden process belonging to HackerDefender Rootkit. Here is another snapshot of SpyDLLRemover detecting […]
You are browsing archives for
Category: Rootkits
RootkitAnalytics is Live Now
Finally RootkitAnalytics is on the world net now. Rootkit Analytics [RA] – the science of rootkit analysis, is a web-portal sculptured to enhance research, analysis and development of rootkit defense mechanisms. I am one of the lead member of RootkitAnalytics along with Ryan. Ryan specializes in Linux based rootkit analysis while I focus on Windows […]
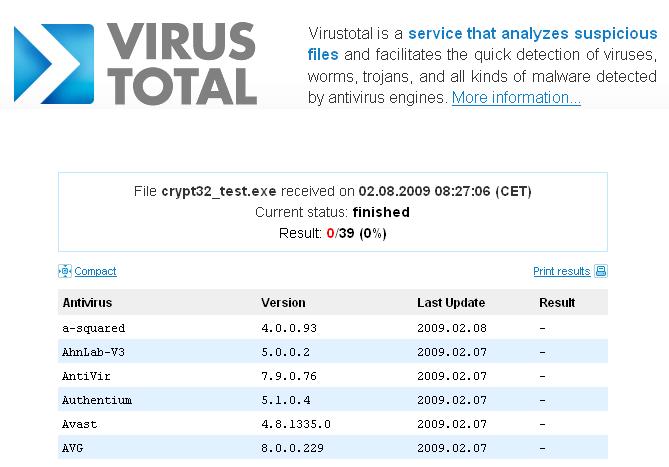
Online Virus Analysis
Now a days it is very common get infected even if you have best antivirus software installed with latest signatures. One of the main reason being is the rise in new category of viruses which does not belong to any previously detected virus families. Also the virus writing has become money making business rather than […]
Book of the month : ROOTKITS
This is the incredible book ever written on darkest area of computer security world. Authors have done splendid job in presenting the most mysterious subject of computer security in very simple and easy to understandable format. . . Here is the detailed table of contents…. 1. Leave No Trace. Understanding Attackers’ Motives. What Is a […]
Detecting & Defeating the Debuggers
Debuggers are the main tool used in reverse engineering. It is used by serial crackers to break the software protection or to uncover the algorithm used in the proprietary applications. On the other hand it is also used by researchers to analyze the malwares. Detecting the presence of debuggers is an important step in this […]