My new tool, SpyDLLRemover is released on the RootkitAnalytics website. This tool helps in detecting and deleting userland based rootkits which hide the processes and injected modules to prevent their detection from antirootkit softwares.
Here is the snapshot of SpyDLLRemover detecting the hidden process belonging to HackerDefender Rootkit.
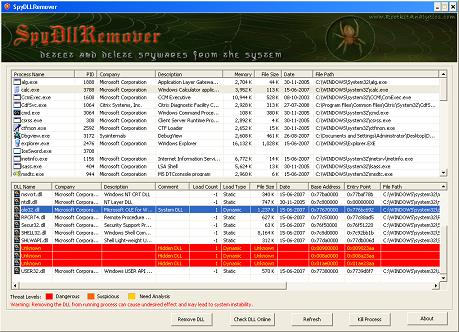
Here is another snapshot of SpyDLLRemover detecting the hidden modules/DLLs loaded by Vanquish Rootkit.
Here is the complete feature list of SpyDLLRemover
————————————————————–
- Detect hidden userland rootkit processes using multiple techniques such as
- Detect the hidden DLL/module within process by using loaded list traversal technique.
- It uses the direct system calls to perform process related operations which defeats any attempt to hide by userland rootkits.
- Separate out the modules/DLLs based on the various threat levels such as hidden dll, BHO plugin dll, and system dll, AppInit DLL etc that makes it effective to detect malicious modules.
- DLLs are marked with different color based on threat level, which makes it easy and quick to eliminate the spyware DLLs.
- It presents state of art technique for Removing the DLL from Remote Process based on DLL Injection method to completely unload the DLL in just one click.
- Terminate any suspicious or hidden process directly using NT system calls.
- It has integrated online verification mechanism through ProcessLibrary.com to validate any suspcious DLLs.
- Displays detailed information about all running processes on the system
- Shows detailed information about each loaded DLLs within process to make it easier for manual analysis.
- It is standalone tool which can be executed directly as it does not require any installation.
– Direct NT System Call Implementation
– Process ID Bruteforce Method (PIDB) as first used by BlackLight
– CSRSS Process Handle Enumeration Method
This makes it easy to differentiate between the spyware & legitimate DLLs.
– Process name
– Process Id
– Company Name
– Process Description
– Memory Utilization
– Process Binary Path
– Process File Size
– File Install Date
– DLL Name
– Company Name
– Description
– Comment about type of DLL (System, Hidden, Suspicious)
– Load/reference count of DLL
– Loading Type (static/dynamic)
– DLL File Size
– File Install Date
– Base Address of DLL
– Entry point of DLL
– Full DLL File Path
————————————————————–
For more information and downloading SpyDLLRemover please visit the RootkitAnalytics website.
.


No Comments Yet