This may sound like another hacking book written to sell, but it is not. This is one such book where author has covered everything from tip to toe of vulnerability exploitation, a complex topic to comprehend, in a simple and practical way.
At a top level this book covers the following topics from security arena…
- Programming
- Exploitation
- Networking
- Shellcode
- Countermeasures
- Cryptography
This book takes the step by step approach to present the art of exploitation to novice and experts alike in a very understandable way. It starts with programming in assembly and C from hacker’s perspective. Then it goes into explaining exploitation techniques along with shell code and networking concepts. The cryptography section at the end is most commendable as author has great job done in explaining such complex topic in easy to understandable format.
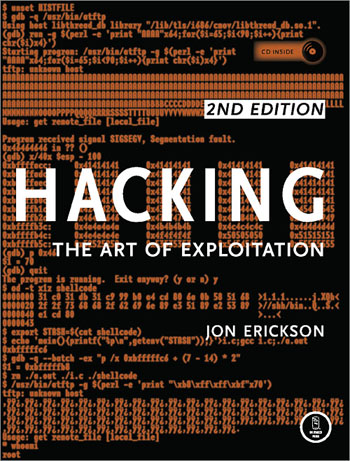
In this second edition, author has introduced new section on Countermeasures which delves into defensive mechanisms against the hacking techniques described earlier in the book. However I liked the cover page of the first edition which had matrix theme.
Overall its the best practical book for any security professional to understand as well as master the art of vulnerability exploitation.
Ebook Download Link: http://www.megaupload.com/?d=HAURV3XB
.

No Comments Yet