Pattern based password recovery is not new concept. However it has been used very rarely in the present day programs besides its importance and improvement it brings on the performance.
It relies on the fact that each of us remembers some part of the password even though we have forgotten the password. This can be any parameters such as length, first few letters, end letters or middle part of the password.Also many of us have habits of choosing all of our passwords of particular pattern. When the person possess certain information about the password, it greatly reduces the time required to recover such a password.
Now the new FireMaster 2.5 introduces this technique which aims to recover the most complex or impossible looking passwords in very realistic time frame and also brings down the recovery time significantly.
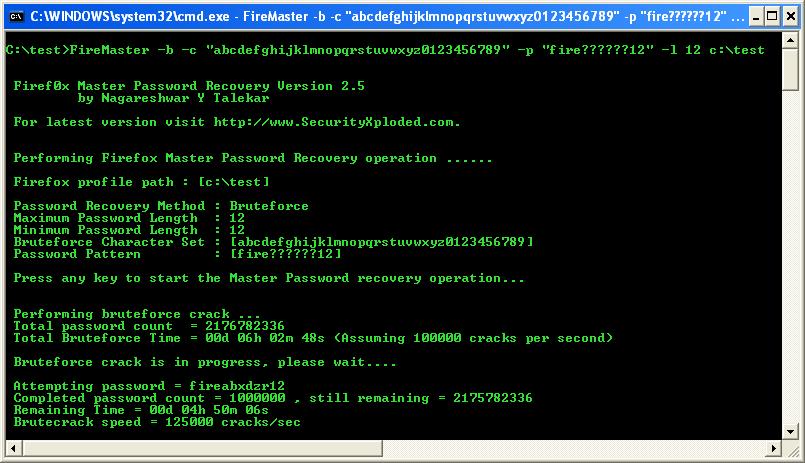
To demonstrate this practically, lets take a example of password with 12 letters containing only lower case alphabets and numbers. Recovering such a password with brute force approach will take months together even on high end machines.
Now assume that certain information about this lost password is available, say for example password is of length 12, begins with ‘fire’ and ends with ’12’.
In this case, running FireMaster using brute force method coupled with new pattern based recovery technique, this impossible looking password can be recovered in just 6 hours….!!!
Isn’t that cool ???
Best result comes when both the tool and the person’s brain are running at their top potential…!
– Nagareshwar
.

thanks for your information …but i have some question to you,what you mean about firefox_profile_path??i hope you explaint to me,,thanks before..(physickers@gmail.com).i will be wait your email
hi,,nagareshwar..
i have recieve your email and i want thanks for you before.
in my firefox,C:\Documents and Settings\\Application
Data\(in here i dont see any file)…
by theway,,i read from magazine about fire password will delete by microsoft,didnt he??.
—– physickers—
indonesia
peace be with you