Process Environment Block (PEB) is a user mode data structure which applies over a whole process. It is designed to be used by the application-mode code in the operating system libraries, such as NTDLL.dll, Kernel32.dll. Through the use of PEB one can obtain the list of loaded modules, process startup arguments, ImageBaseAddress, heap address, check […]
You are browsing archives for
Category: Secure Coding
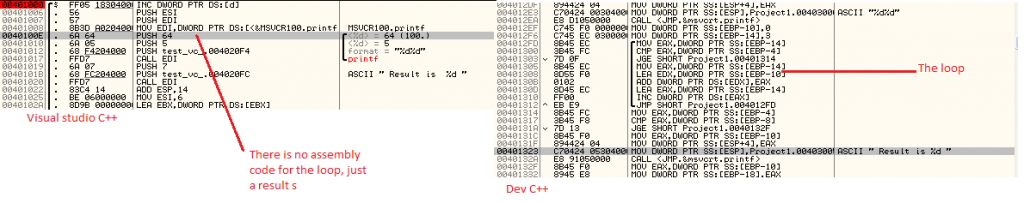
Demystifying Compiler Optimization – Dif
I analyzed some simple source code examples running in visual C++ (without optimization option) and Dev C++. I saw that VC++ code is slightly optimized then DEV C++. The following code shows the difference between function calls on both the compilers. In visual C++: push eax mov ecx, [local.1] push ecx call F Dev C++: […]
Book of the Month – Android in Action
Lately I was looking for the best & latest book on Android programming and after stumbling through many of the Android books on Amazon I finally got exactly what I was looking for! . The best & latest Android book – ‘Android in Action’. The book covers A-Z of Android Programming, starting with basics to […]
CryptoCode: Create SHA256 Hash using Ope...
In the previous CryptoCode series articles, I had written about generating MD5/SHA1/SHA256 hashes, encryption/decryption algorithms using Windows Cryptography functions. Today I am writing about creating SHA256 hash using OpenSSL’s Cryptography Library. OpenSSL is very popular library providing SSL & Cryptography based functions which is consumed by top softwares. OpenSSL library is FREE to use in […]
CryptoCode: Index of All Crypto Articles
Recently I had been writing about code samples for demonstrating the usage of various Cryptography functions such as generating MD5/SHA256 hash generation, encryption of password based on the key, BASE 64 encoder/decoder etc. Here is the index of all those Crypto articles and associated tools. . Crypto Articles CryptoCode: Generate MD5 Hash using Windows Cryptography […]
Crypto Code: Base64 Encoder
In previous posts I had written about Base64 decoder and other hashing algorithms using Windows Cryptography functions. In this post I will write simple C program for BASE64 Encoder. . Due to its simplicity BASE64 has become very popular choice for simple encoding of the passwords or other sensitive data. But due to its trivial […]
CryptoCode: Base64 Decoder
In previous blog posts I had written about MD5 & SHA256 Hash generation algorithms as well as DES Encryption/Decryption methods using Windows Cryptography Functions. Today I am going to present a crypto program for Base64 Decoder – very popular encoding algorithm. . Base64 is commonly used along side the encryption/decryption algorithms as a double layer […]
CryptoCode: DES Encryption & Decryption
In previous posts, I wrote example code for generating MD5 Hash & SHA1 Hash using Windows Cryptography Functions. Here I am going to write about DES encryption/decryption algorithm with SHA1 based Hash key generated using Password. This is most common way of generating password where in unique data is used to generate a Hash Key […]
CryptoCode: Generate SHA1/SHA256 Hash u...
In my previous blog post on ‘Generating MD5 Hash’, I wrote code example on creating MD5 hash. Today I will be presenting the direct code sample for generating SHA1 hash using Windows Cryptography functions. Due to various collision problems with MD5 Hash, now a days SHA256 hash is used more extensively for unique identification. The […]
CryptoCode: Generate MD5 Hash using Win...
Here I have decided to put together series of Crypto sample using Windows Cryptography functions as well as OpenSSL library. This is to make it easier for myself as well as others to find ready to use cryptography code examples. Though some of these code samples are present some where on the net, I am […]