DirectoryScanner is the FREE Directory Server fingerprinting tool. It can help you to remotely detect the type of Directory servers (such as Microsoft Active Directory, Novell eDirectory etc) running on the local network as well as Internet. It is GUI version of RemoteDirDetector– a perl based console tool to detect type of directory servers. . […]
You are browsing archives for
Category: Network Security
Launched NetCertScanner 2011 Edition !
We are pleased announce the launch of ‘NetCertScanner 2011 Edition’. NetCertScanner – the Universal SSL Certificate Scanner – is the enterprise version of our FREE SSLCertScanner Tool. . It is the unique software to scan for SSL services (Web Servers, Directory Servers etc) in your network and find out any of the expired (or about […]
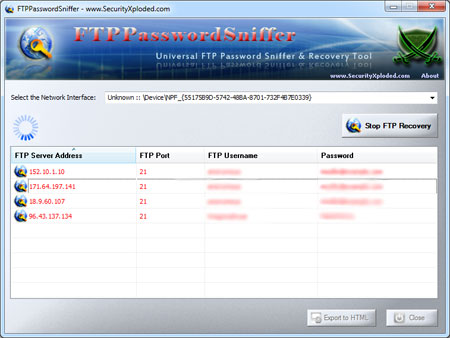
New Tool FTPPasswordSniffer – Universal
FTPPasswordSniffer is the universal FTP password recovery tool for any of your favorite FTP application such as FileZilla, SmartFtp etc. It can not only recover the lost FTP account password but also can sniff and catch any of the FTP account passwords passing through your network, thus making it a great tool for Penetration Testers. […]
Launched NetCertScanner – First Enterpri
NetCertScanner is a Enterprise version of our recently released free tool, SSLCertScanner which was meant only for personal use or for the needs of smaller organizations. NetCertScanner has all the professional level features and wide range of support options required for medium/bigger Enterprises who generally has to manage large number of SSL services in their […]
Book of the Month – CISSP All-in-One Exa
I have been writing review for many technical security books in the recent past, so this time I thought of picking up certification related book. I generally don’t value these security certifications. Though these certifications do not add any greater value to ones technical knowledge but they certainly help anyone in getting ahead in the […]
Unleashing VASTO – A Virtualization Asse
VASTO is the first of its kind toolkit designed to asses the security of various Virtualization solutions including VMWare and Xen server. It is implemented as set of modules which can be integrated into Metasploit , the popular penetration testing framework. This makes it very easy for pen testers to directly integrate VASTO with their […]
Book of the Month: Cloud Security & Priv
Other day while I was crawling through the books at the local book mall, I just ran into this book. Immediately I popped up amazon site on my cell to check the ratings and found that its rated 4.5 (out of 11 ratings) which is a signal for must buy. Cloud computing being the hot […]
Delivered Talk on ‘Application Virtualiz
I just came back after delivering presentation on ‘Application Virtualization’ during ‘Clouding Computing & Virtualization‘ summit at NITK Surathkal, one of the premiere engineering institute in India. It was great moment for me to deliver the talk at my own college after 6 years of passing out from here. The event was organized as educational […]
Book of the Month – VIRTUAL HONEYPOTS
Honeypots have been the best mechanism to trace the real security threats in the wild whether it may be hacker attacks, worms or botnets. In today’s world, where deploying and setting up physical honeypots are not only complex but also costly in terms of time and money, virtual honeypots helps in great extent by making […]
Book of the Month – Wireshark Network An
“Wireshark Network Analysis” is the latest book on Wireshark, the top notch tool for network analyzer.Wireshark is used in analyzing network traffic, troubleshooting network problems on wired and wireless network. Either you are an network analyst, administrator, network security professional this will be the book that you don’t want to miss. The book is well […]