Here is the quick update on this month’s Local Security meet (SX/Null/G4H/owasp) where Amit Malik delivered a superb session on analysis of Botnets with practical case study. This is part of our FREE ‘Advanced Malware Analysis Training’ series started from Dec 2012. In this session Amit Malik explained various advanced stealth techniques including command & […]
You are browsing archives for
Category: Debugging
Training Session Part 7 – Practical Reve
Here is the quick update from our this month’s Local Security meet (sx/null/g4h/owasp) where Nagareshwar did splendid session on ‘Practical Reversing (II) – Unpacking. This is part of our ongoing FREE ‘Reversing & Malware Analysis Training’ started since our Jan 2012 meet. In this interesting practical session, he demonstrated How to manually unpack UPX packed […]
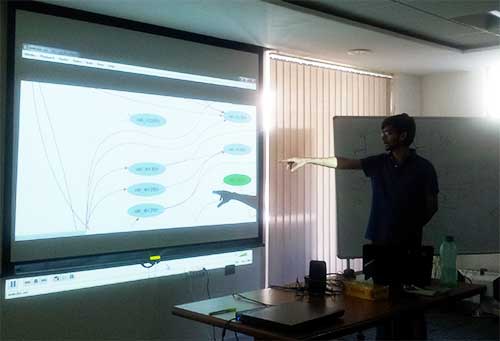
Assembly Programming Basics Presentation...
Here comes the update from our last local security meet (sx/null/g4h/owasp) where Amit Malik & Swapnil delivered spectacular session on ‘Assembly Programming Basics’. This is part of our ongoing FREE ‘Reversing & Malware Analysis Training’ which has been started since our last meet. Duo delivered superb one hour session to jam packed 40+ folks who […]
Book of the Month – IDA PRO 2nd Edition
The best book on IDA PRO gets even better with second edition. This is one of those special books which does not need any review at all. The book stands on its own. . Since I have received the request from No Starch Press for special review of this book, here I will make an […]
Released DllHijackAuditor v2 with New &
DllHijackAuditor is the FREE tool to Audit against the DLL Hijacking Vulnerability for any Windows application. This is recently discovered critical security vulnerability affecting most of Windows systems. Currently large number of applications are currently susceptible to this vulnerability which can allow any attacker to completely take over the system. . In the first version […]
Best Compiled List of WinDbg Commands
While crawling on the net for good list of Windbg commands, I have come across this site which has grouped together all essential commands. This makes it very easy to quickly figure out the required commands while you are deep into debugging… Here is the link to the page http://www.windbg.info/doc/1-common-cmds.html It is also available in […]