Here is the quick update on this month’s Local Security meet (SX/Null/G4H/owasp) where Amit Malik delivered a superb session on analysis of Botnets with practical case study.
This is part of our FREE ‘Advanced Malware Analysis Training’ series started from Dec 2012.
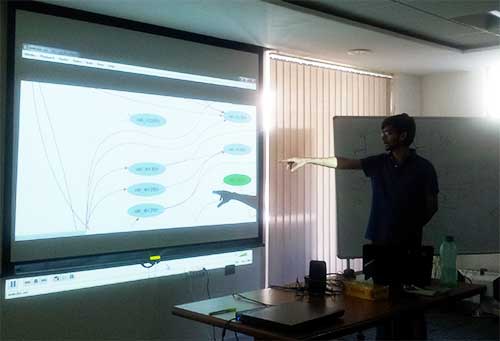
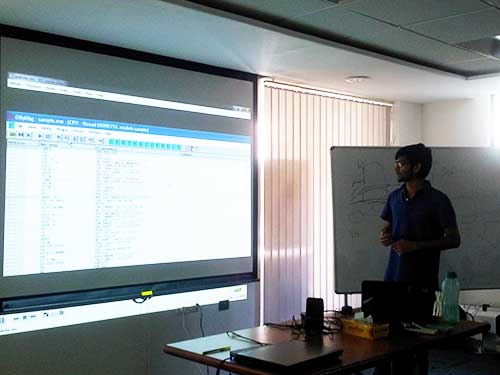
In this session Amit Malik explained various advanced stealth techniques including command & control mechanisms used by Botnets. At the end, he presented case study of Waledac Botnet – one of the top 10 sophisticated botnets – along with video demonstration.
This presentation is available at our Security Presentations page. Demo Videos for all the sessions are available on Security Training Videos page.
We extend special thanks to ‘Amit Malik’ for delivering one of his finest and most enjoyable session.
Stay tuned to our next and yet another exciting training session !


No Comments Yet