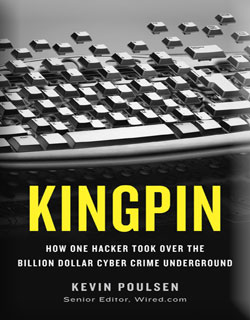
Here is the yet another but superb and thrilling real tale from the Hackers underground, “KINGPIN – How One Hacker Took Over the Billion-Dollar Cybercrime Underground”
.
In this exciting & entertaining story from cyber underground – Kevin Poulsen – the former hacker & investigative editor of wired.com – reveals every account of covert criminal operation as it happened on the field.
.
.
Here is the core information about the book,
- Title: Kingpin – How One Hacker Took Over the Billion-Dollar Cybercrime Underground
- Author: Kevin Poulsen
- Publisher: Crown
- Hardcover: 288 pages
- Release Date: February 22, 2011
- Rating(Amazon):

.
In KINGPIN, Kevin tells the story of Max Vision, a white hat computer hacker who turned to the dark side. Among other things, Max stole credit card data — “dumps” — on millions of consumers, which he sold in bulk to a card counterfeiter named Chris Aragon. In this excerpt, a new discovery gives him a chance to expand his operation.
.
Book exposes scary story of how online hackers stocked credit card numbers, fake checks, hacked bank accounts to make millions overnight through well structured ring of criminals operating from dark corners of world. It showcases how attackers used advanced techniques such as remote execution exploits, smart phishing sites, Trojans, advanced keyloggers to sweep the innocent victims around the world and transferred bounties under the nose of security guards from top banks. A good case study for Howard folks to ponder into.
.
Once you take this book in your hand, it is hard to put down until the end !
.
Here are few random lines from the excerpt of this book from wired.com
.
In June 2006, a stroke of good luck gave him a chance to expand. A serious security hole emerged in the software RealVNC a remote-control program used to administer Windows machines over the internet.
It was a simple matter to modify a VNC client to always send back type 1, turning it into a skeleton key. An intruder like Max could point his hacked software at any box running the buggy RealVNC software and instantly enjoy unfettered access to the machine.
Max started scanning for vulnerable RealVNC installations as soon as he learned of this gaping hole. He watched, stunned, as the results scrolled down his screen, thousands of them: computers at homes and college dorms; machines in Western Union offices, banks and hotel lobbies. He logged into some at random: in one, he found himself looking at the feeds from closed circuit video surveillance cameras in an office building lobby. Another was a computer at a Midwest police department, where he could listen in on 9-1-1 calls. A third put him in a home-owner’s climate control system; he raised the temperature 10 degrees and moved on.
Continue reading this interesting excerpt here and you will be tempted to buy !
.
eBook Link : http://www.filesonic.in/file/373347771/0307588688.rar

No Comments Yet