We have been busy working on lot of things amid of next major release of SpyDLLRemover as mentioned in previous posts. We also planned for minor update on StreamArmor. Here is the brief update on each of these tools.
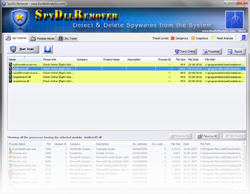
SpyDllRemover 4.0
We were right on schedule for last week mega release of SpyDllRemover but due to out of band work on our new tool, DllHijackAuditor we had to postpone the release for a while. Mainly for the two big reasons, one is to add DllHijackAuditor functionality straight into SpyDllRemover itself so that user don’t have to look for another tool for auditing their applications for Dll Hijack Vulnerability. Next one is to have more process based heuristics to detect most of the Spyware processes (which are not necessarily Rootkits i.e they are not hidden but difficult to distinguish).
.
.
With all these coming together, the expected release of SpyDllRemover 4.0 will be around the end of this month. We also have to plan to make a early beta release so that user can get the preview of it as well as report any issues to make it a clean release.
StreamArmor 1.1
We have received couple of minor issues with StreamArmor, so we have decided to give it a quick fix along with some small usability changes. We have also seen and heard about important issue i.e system is getting slow down during the scanning operation due to StreamArmor becoming more processor intensive. We are also working on this but we don’t have any concrete solution yet.
If you have any suggestions/links on how to prevent application from slowing down the system during the operation (this is typical issue with Antivirus/Antispyware scanners), do let us know. Any pointers on this, will be definitely helpful.
StreamArmor 1.1 will be possibly out in next few days unless we decide to give full fix for system slow down issue.
.
Thanks for everyone who had send the error reports/suggestions which has helped us to make these tools better than earlier.
.
.

No Comments Yet